Edge Computing Strategies to Strengthen Cybersecurity in Web Development Apps
Reduce data exposure risks by moving AI processing to devices, with programming tutorials on secure web development practices amid rising cloud vulnerabilities.

Edge Computing Strategies to Strengthen Cybersecurity in Web Development Apps
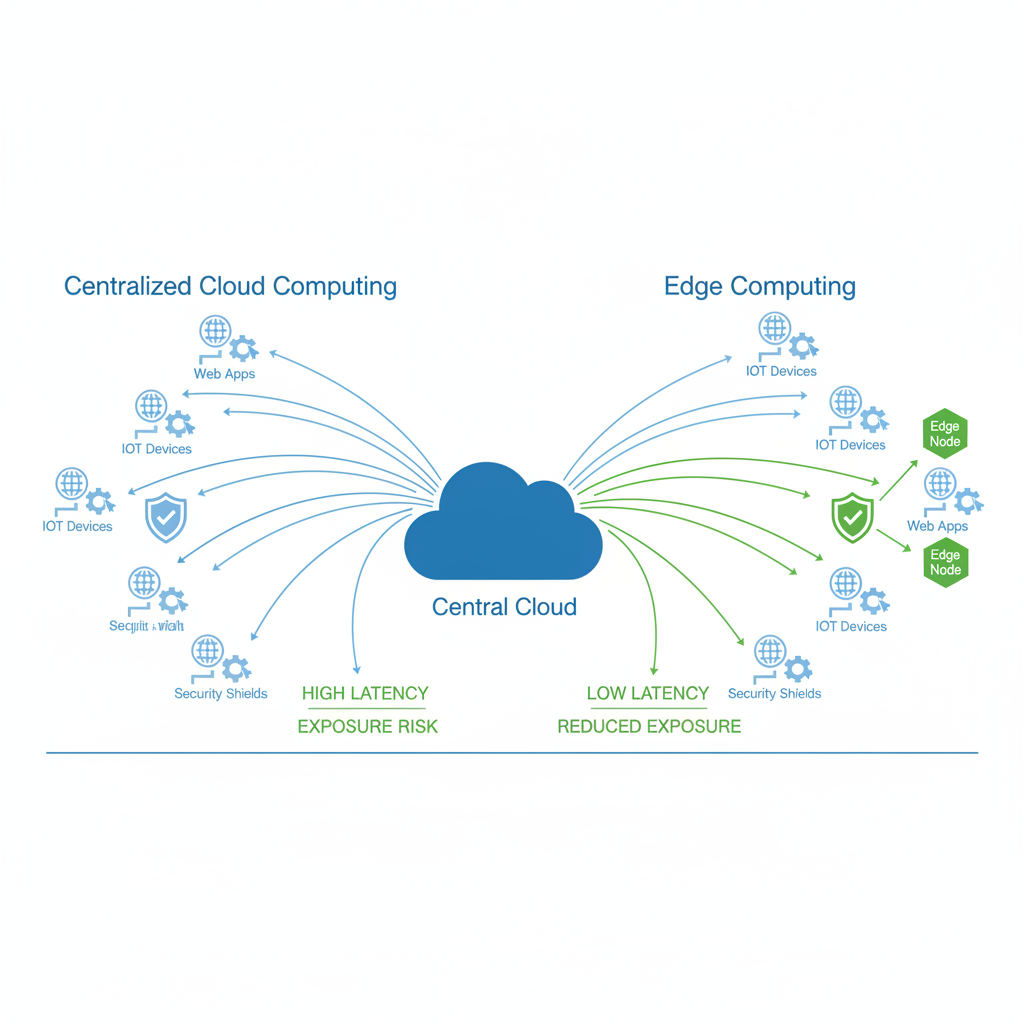
What if edge computing could transform cybersecurity in your web development apps, slashing data exposure risks from centralized cloud computing by processing sensitive data right at the edge?
By the end, you'll master a holistic strategy blending edge computing with secure coding and edge AI. You'll get programming tutorials to implement robust defenses against cyber threats. That way, you can build resilient web applications.
What Is Edge Computing and How Does It Boost Cybersecurity for Web Apps?
Edge computing processes data close to its source. Think devices or local servers, not distant centralized clouds. This matters big time for web development. Real-time apps handling user interactions or IoT feeds churn out massive data volumes. Billions of IoT devices are out there now, and those numbers keep climbing. All that data needs handling without constant trips to the cloud.
In web apps, edge computing cuts latency by keeping things local. That directly strengthens security. Data doesn't travel networks as much, so the window for interception shrinks. Centralized clouds? They're single points of failure. One breach exposes it all. Edge setups spread the risk. User authentication or payment processing can happen on edge nodes. Less sensitive info gets transmitted. Plus, processing at the edge speeds up real-time decisions.
You see this in web apps with dynamic content. Edge nodes filter and analyze inputs before any cloud handoff. Breach surfaces get smaller. Developers control data flows better, making it tougher for attackers to hit transit weak spots.
How Edge AI Cuts Data Exposure in Web Apps
Edge AI pushes it further. It runs machine learning models right on edge devices. Data gets processed without uploading to the cloud. Sensitive info stays off public networks. That's a huge cut in exposure risks. Artificial intelligence on the edge improves decision-making by handling data locally.
Take anomaly detection. An edge AI model checks login patterns or traffic spikes at the browser or gateway. Suspicious stuff? It blocks it without cloud help. Real-time encryption works the same. AI gauges threat levels and tweaks keys instantly. Compare to cloud reliance, where every packet risks man-in-the-middle attacks on exposed routes.
Edge devices have risks. They're distributed with lighter defenses. But edge AI fights back with proactive moves. In web apps, attack vectors shrink. Data in transit plummets. AI boosts functionality but adds challenges. The win? Apps spot intrusions quicker. User data stays at the edge unless absolutely needed.
To make this concrete, picture a fitness app tracking user health data. Edge AI on the user's phone analyzes patterns for anomalies like unusual heart rates signaling a hack attempt. No need to send raw biometrics to the cloud. Decisions happen fast, privately.
Top Secure Coding Practices for Tough Web Applications
Secure coding is the backbone. It stops exploits edge computing can't touch alone. Common vulnerabilities? SQL injection, XSS, command injection.
Here are key practices to build from the ground up:
- Input validation and sanitization: Check every user input against whitelists. Reject bad stuff outright.
- Parameterized queries for database calls. Blocks SQL injection cold.
- No hardcoded credentials. Use environment variables or secret managers.
- Enforce HTTPS with SSL/TLS for encrypted client-server chats.
- Secure headers like Content-Security-Policy to fight XSS.
- Least privilege: Services access only what they need.
- Third-party libraries? Trusted sources only. Verify with hashes. Update regularly.
Secure coding spreads awareness with layers of checks. Layer them: Validate at the edge, sanitize backend, encrypt all over.
Expand on input validation. Say a contact form. Whitelist allows only letters, numbers, @ symbols. Anything else? Bounce it. Pair with server-side checks for double defense. This stops injection attacks before they start.
Why Edge Computing and Secure Coding Team Up Perfectly
Pairing edge computing with secure coding? It's synergy. Each amps the other. Edge handles initial validation locally. Secure code nails app logic edge cases. AI threat detection plus hardened code covers everything.
Think e-commerce app under DDoS and theft pressure. Edge nodes use AI to drop malicious traffic early. Secure coding hits survivors with parameterized queries and XSS shields. Attack surface? Tiny. Less data goes central, and the rest is locked down.
Edge devices skip updates sometimes, upping risks. Secure coding adds verification everywhere. Result: Real-time responses, threats killed at multiple spots. No single flaw tanks it all.
Real-world example: A banking app. Edge processes login biometrics locally with secure code validating sessions. If AI flags odd behavior, it locks out without cloud ping. Customers feel the speed and trust the privacy.
Programming Tutorial: Deploy Edge AI for Cybersecurity in Web Development
Ready to code? Grab TensorFlow Lite for lightweight models or ONNX for compatibility. They run smooth in browsers via WebAssembly.
Set up: npm install @tensorflow/tfjs-tflite. Train a basic anomaly model on traffic data. Public datasets work for starters. Convert to Lite with TensorFlow tools.
Integrate via service workers for edge processing. Here's a starter snippet:
self.addEventListener('fetch', event => {
event.respondWith(handleRequest(event.request));
});
async function handleRequest(request) {
const data = await request.json();
// Input validation (secure coding)
if (!validateInput(data)) {
return new Response('Invalid input', { status: 400 });
}
// Load TFLite model
const model = await tflite.loadTFLiteModel('model.tflite');
const inputTensor = tf.tensor2d([data.features]);
const output = model.predict(inputTensor);
const prediction = await output.data();
inputTensor.dispose();
output.dispose();
if (prediction[0] > 0.8) { // Anomaly threshold
logThreat(data.ip, 'Anomaly detected');
return new Response('Access denied', { status: 403 });
}
return fetch(request);
}
function validateInput(data) {
return data.ip && typeof data.features === 'object' && data.features.length === 10;
}
function logThreat(ip, reason) {
// Secure logging: no sensitives
console.log(`Threat from ${ip}: ${reason}`);
// Anonymized backend alert
}
This handles requests at the edge. Validates inputs securely. Logs threats without raw data leaks. Deploy on CDN with HTTPS. Test attacks, watch latency drop.
Level up to WebAssembly. Compile C++ AI to WASM with Emscripten for heavier lifts. Train your model on Kaggle datasets like network intrusion logs. Fine-tune thresholds based on false positives in tests. Add more features: User agent checks, geolocation filters. This turns your web app into a fortress.
Pro tip: Monitor model drift. Edge environments change; retrain periodically with edge-collected data sent anonymously to cloud.
Challenges and Fixes for Edge Computing in Secure Web Dev
Edge isn't perfect. Devices have resource limits. Optimize models: Prune networks, quantize with TensorFlow Lite tools. Shrinks size, keeps accuracy.
Scalability? Hybrid setups. Edge takes hot data, cloud aggregates. Security holes? Edge misses updates. Fix with auto firmware and mutual TLS auth.
Distributed nature ups vulnerabilities. Embed secure coding day one. Multiple layers. Central dashboards for anonymized logs.
AI adds challenges too. Stick to trusted libraries, update often. These steps make edge production-ready for web apps.
Dive deeper into quantization. It significantly reduces model size, runs on phones without choking. Test accuracy pre/post to minimize degradation. Hybrid helps scale by processing much traffic at the edge and using the cloud for ML tasks where needed.
Implement these edge computing cybersecurity tactics today. Future-proof your web development apps. Try one tutorial. Measure risk drops. Stay ahead in this AI-driven world. Grab the full code repo here or drop your edge stories in comments.
Related Articles

PAN-OS GlobalProtect CVE-2026-0257 Active Exploitation Steps for DevOps Teams

Cybersecurity Risks in Multi-Agent AI Systems: Defending Against Deepfake Attacks

Hybrid Cloud Deployment Models for Banks Handling Regulated Data
